Developer posts
40 posts in the Developer category.

Three serious API paradigms, three different shapes. We compare schema definition, network footprint, tooling, and which problem each one was actually designed to solve.

Those six-digit codes from Google Authenticator, Authy, and 1Password are not magic. They're HMAC over a clock. Here's the precise algorithm, the security model, and why drift handling matters.

Whisper handles 99 languages, accents, background noise, and code-switching better than anything before it. We unpack the encoder-decoder transformer architecture that made it possible.

TypeScript is now the default for serious JS projects, but it's not free. We weigh the cost of static typing, the value at scale, and pragmatic rules for choosing per-project.
JSON Schema gives you contract-driven validation for any JSON payload. We walk through the spec, the keywords that matter, and how it powers OpenAPI and Zod.

Generating TypeScript interfaces from a JSON sample looks like magic, but it's a careful walk through structural inference. We explain the rules these tools use and when they get it wrong.

LCP, INP, CLS, TTFB — the alphabet soup of web performance. We explain what each metric measures, what passes the bar, and how to actually move your scores up.
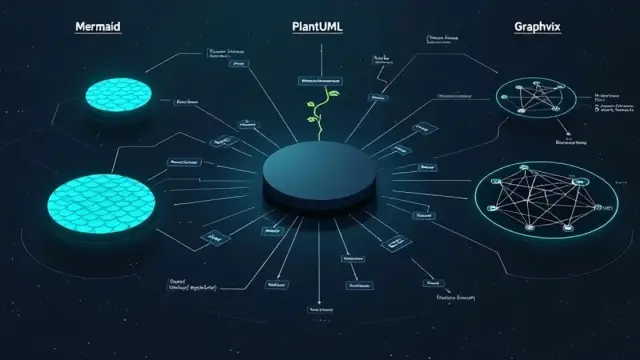
Three popular diagram-as-code tools, three different philosophies. We compare syntax, layout engines, output quality, and which one fits your README versus your architecture doc.

Browsers don't have a Python interpreter. So how do online Python runners work? The answer is WebAssembly and a project called Pyodide. Here's the full story.

When monotonic auto-increment IDs break at scale, Snowflake IDs step in. We unpack the 64-bit layout, clock-skew problems, and why every major distributed system has its own variant.

Random IDs are everywhere, but the trade-offs differ. We compare collision odds, sortability, length, and database performance for the four most common modern ID schemes.

API keys are the workhorse of server-to-server authentication, but a leaked key can mean thousands of dollars in fraudulent charges. Here's how they actually work, where to store them, and how to design rotation that survives contact with reality.
If a Slack message that contains '10.0.0.0/16' makes you nod and quietly Google 'what does /16 mean again', this is the post for you. Read /24, /16, and /28 without the binary math.

CSP is the most powerful XSS defense most sites either don't use or deploy wrong. Here's what it actually stops, what it doesn't, and how to ship a working policy without breaking everything.

JSON, YAML, and TOML each solve a different problem — but pick the wrong one and you'll spend Friday night chasing a whitespace bug. Here's the honest comparison with a decision matrix you can actually use.

Every developer searches the same MDN regex page over and over. This is the reference you skim when you already know the concept and just need the syntax — including the gotchas that bite in 2026.

Webhooks are deceptively simple — until your handler processes the same charge twice or accepts a forged event. Here's the production reality: HMAC signing, idempotency, backoff, and replay defense.

HTTP caching is one of the most powerful and most misunderstood web performance tools. Getting Cache-Control right can eliminate most of your server's traffic for static assets.
CSS minification strips out whitespace, comments, and unnecessary characters without changing any rules. On large stylesheets the savings are significant, and the tooling is trivial to set up.
Web fonts are one of the most common sources of layout shift and invisible text flash. The font-display property and a few preload hints can eliminate both problems.
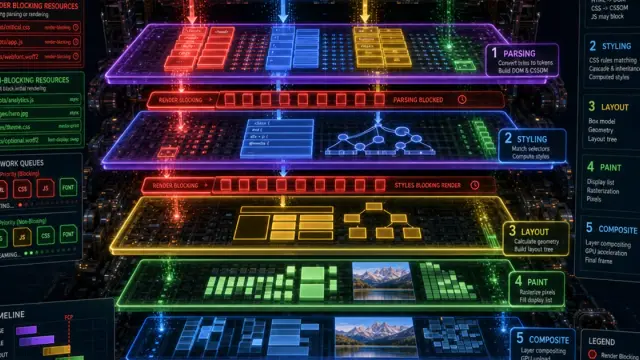
The critical rendering path is the sequence of steps a browser must complete before showing the first pixel. Optimizing it is one of the highest-impact things you can do for perceived performance.
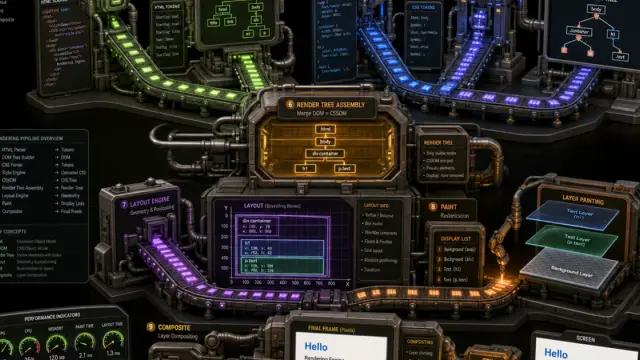
A browser takes HTML, CSS, and JavaScript and turns it into pixels. The steps between those two points — parsing, layout, painting, compositing — directly affect performance and user experience.
CSS custom properties are far more powerful than SASS variables — they are live, inheritable, and can be changed with JavaScript at runtime. Here is everything you need to know to use them well.
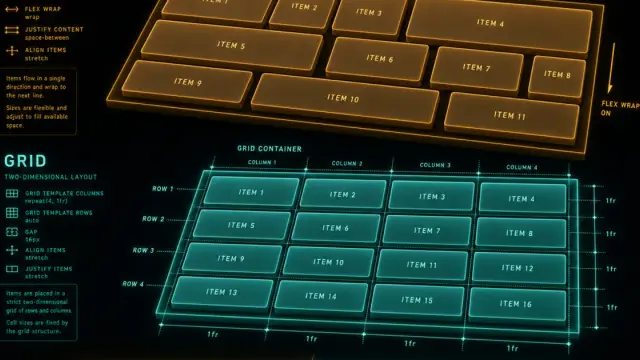
Flexbox and Grid are not competing technologies — they solve different layout problems. Knowing which to reach for makes your CSS cleaner and your layouts more robust.
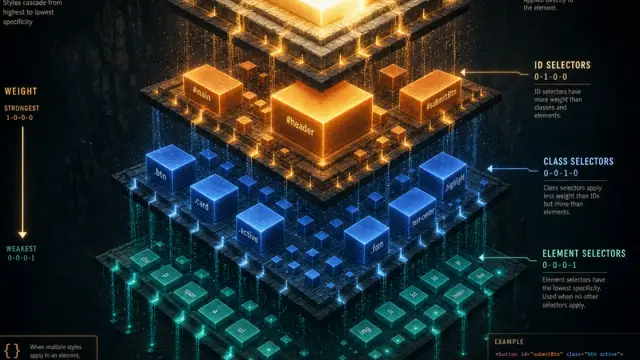
CSS specificity is the invisible rule that decides which style wins when two selectors target the same element. Understanding it lets you debug style conflicts without resorting to !important.

You type a domain and a page loads — but between those two events is a surprisingly elegant distributed lookup system. Here is exactly what happens at each step.
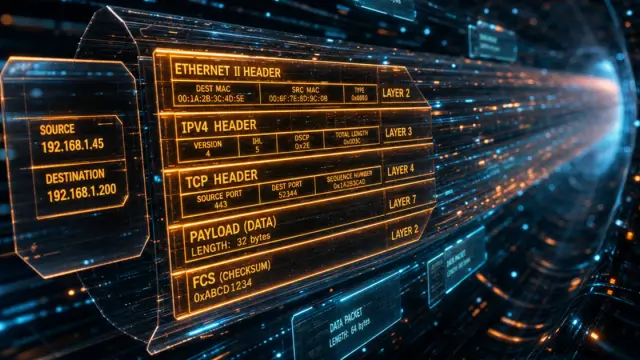
HTTP headers carry critical information about authentication, caching, content type, and security — yet many developers only interact with them when something goes wrong. This reference covers the most important ones.

A hardcoded API key committed to a public repo is a nightmare that keeps on giving. Here is a practical guide to managing environment variables and secrets safely across environments.
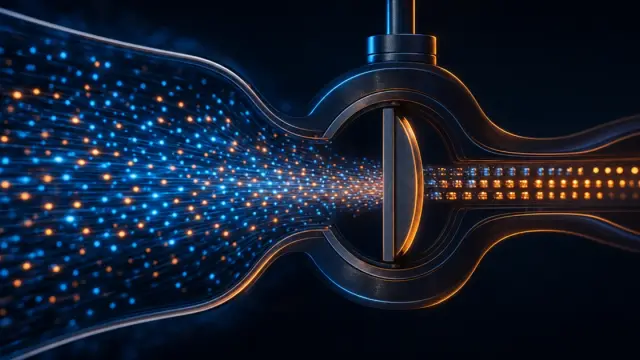
Rate limiting is invisible when it works and infuriating when it is misconfigured. Understanding the underlying algorithms helps you implement limits that protect your API without frustrating legitimate users.

OAuth 2.0 is the standard behind every "Sign in with Google" button — yet the underlying flow confuses many developers. This post maps out exactly what happens behind the scenes.
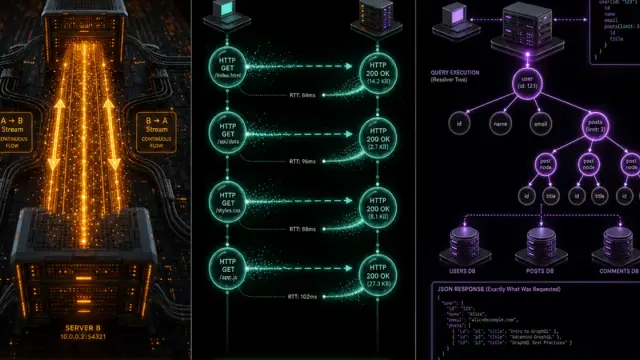
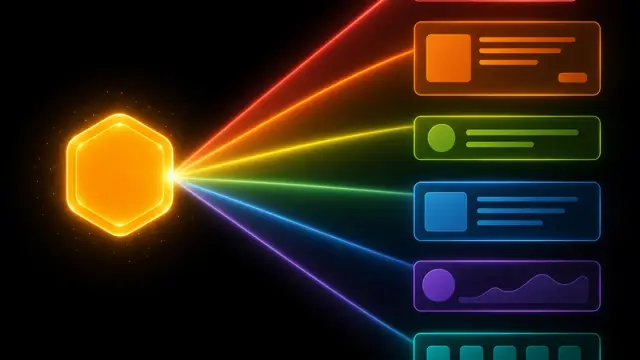
REST, GraphQL, and WebSockets each solve a different category of problem. Picking the wrong one adds complexity without benefit. Here is how to think through the choice for your specific use case.
CORS errors block your frontend from talking to your own API — and the fix is not to disable it. Understanding why browsers enforce the same-origin policy makes the solution obvious.
MD5 and bcrypt are both called hashing algorithms, but they serve completely different purposes. This guide explains what makes a hash function suitable for checksums versus password storage.

A space in a URL becomes %20, a plus sign becomes %2B — but not always, and the rules differ depending on where in a URL you are. This post explains the why and the how of percent-encoding.
Base64 shows up everywhere from JWTs to CSS data URIs to HTTP Basic Auth — but it is often misunderstood. Here is a clear explanation of what it actually does and when it makes sense to reach for it.

Regex has a reputation for being cryptic, but once you understand a handful of building blocks, even complex patterns become readable. This guide takes you from zero to confidently writing your own expressions.

Is that a 401 or a 403? A 404 or a 410? HTTP status codes have precise meanings that most developers only half-remember. Here is the definitive guide with practical guidance on when to use each.

A badly designed API is a source of endless frustration. These battle-tested REST API design principles help you build endpoints that are intuitive, maintainable, and future-proof.

A JWT looks like random text until you decode it — then you find a header, a payload, and a signature. This post explains exactly what each part does and why that matters for security.
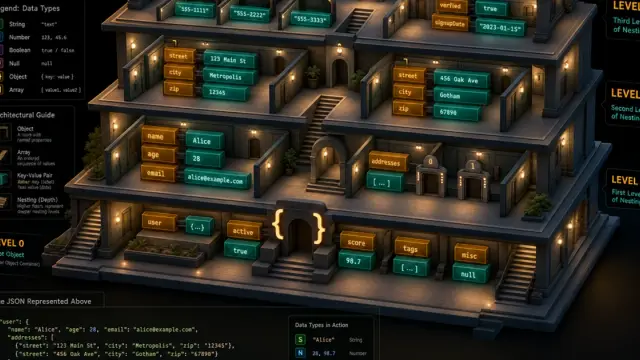
JSON is the lingua franca of modern web APIs, but its deceptively simple syntax trips up beginners in subtle ways. This guide walks through every rule with practical examples.