Calculators posts
14 posts in the Calculators category.
Time in the market beats timing the market — but only if you understand the math. We compare lump-sum compounding, monthly SIP, and employer-matched 401(k) contributions.

The avalanche method always wins on math. The snowball method usually wins on follow-through. We weigh both, run the numbers on a $24,500 four-debt scenario, and explain why both methods exist.

Most fitness watches use percent of max HR. Karvonen factors in your resting rate. We explain why that matters, what each zone actually trains, and how to set yours correctly.

Why is most of your early payment going to interest? We work through the amortization formula step by step, build the schedule from scratch, and show what extra payments really do.

Every fitness app guesses your calorie target the same way: BMR formula, activity multiplier, macro split. We open the black box and show what each variable actually means.

Every HTTPS handshake, every code-signing check, every TLS-secured email rests on X.509. We dissect the fields, extensions, chain of trust, and what each section actually does.
A checksum is a small number computed from a block of data that lets you verify the data has not changed. Here is why this simple idea underpins file downloads, network protocols, and storage systems.

Every HTTPS connection starts with a TLS handshake — a sub-second ceremony that establishes identity and agrees on encryption keys. Here is the full sequence in plain English.

The magic behind HTTPS, SSH, and PGP encryption is public key cryptography — a system where you can encrypt a message that only the intended recipient can decrypt. Here is how it works.
Unix timestamps are just numbers — the count of seconds since January 1, 1970 UTC. But timezone handling, milliseconds vs seconds, and the 2038 problem all add complexity that catches developers off guard.

Binary is not just for low-level programming — it shows up in bitmasks, permissions, color values, and network addresses. This guide makes number base conversion intuitive rather than mechanical.
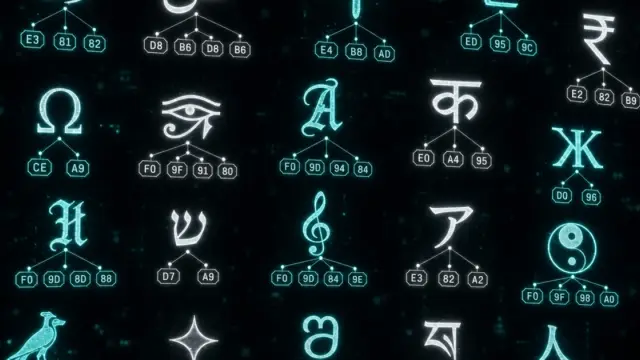
Every string in your program is ultimately bytes. Understanding how Unicode maps characters to code points and how UTF-8 encodes those to bytes prevents a whole class of subtle bugs.

Treating Base64 as encryption or MD5 as a secure hash are among the most common security mistakes developers make. This post draws a clear line between encoding, encryption, and hashing.
Math.random() and /dev/urandom look similar but are fundamentally different. One is suitable for games, one for cryptography. Understanding why that distinction matters prevents serious security mistakes.