UtilityKit Blog
Guides, deep dives, and explainers for developers and curious minds.

JSON is the lingua franca of modern web APIs, but its deceptively simple syntax trips up beginners in subtle ways. This guide walks through every rule with practical examples.
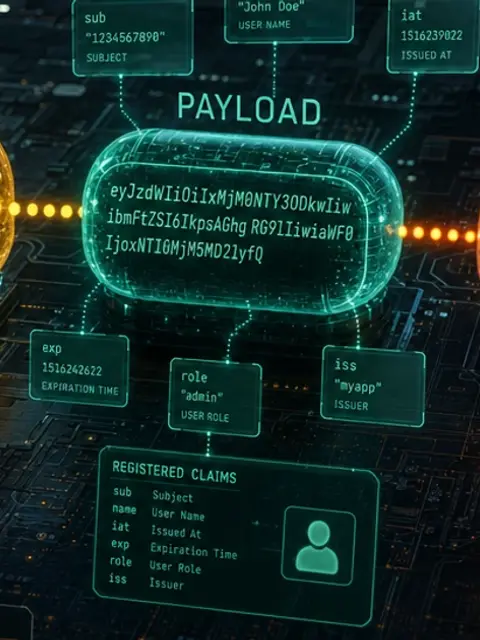
A JWT looks like random text until you decode it — then you find a header, a payload, and a signature. This post explains exactly what each part does and why that matters for security.

A badly designed API is a source of endless frustration. These battle-tested REST API design principles help you build endpoints that are intuitive, maintainable, and future-proof.

Is that a 401 or a 403? A 404 or a 410? HTTP status codes have precise meanings that most developers only half-remember. Here is the definitive guide with practical guidance on when to use each.

Regex has a reputation for being cryptic, but once you understand a handful of building blocks, even complex patterns become readable. This guide takes you from zero to confidently writing your own expressions.
Base64 shows up everywhere from JWTs to CSS data URIs to HTTP Basic Auth — but it is often misunderstood. Here is a clear explanation of what it actually does and when it makes sense to reach for it.

A space in a URL becomes %20, a plus sign becomes %2B — but not always, and the rules differ depending on where in a URL you are. This post explains the why and the how of percent-encoding.
MD5 and bcrypt are both called hashing algorithms, but they serve completely different purposes. This guide explains what makes a hash function suitable for checksums versus password storage.
CORS errors block your frontend from talking to your own API — and the fix is not to disable it. Understanding why browsers enforce the same-origin policy makes the solution obvious.
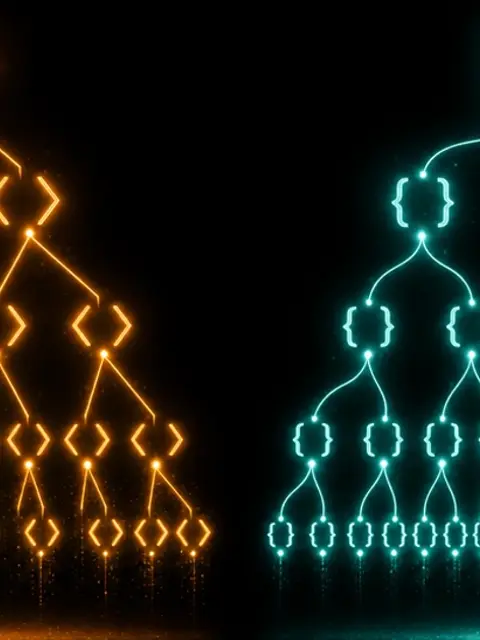
REST, GraphQL, and WebSockets each solve a different category of problem. Picking the wrong one adds complexity without benefit. Here is how to think through the choice for your specific use case.

OAuth 2.0 is the standard behind every "Sign in with Google" button — yet the underlying flow confuses many developers. This post maps out exactly what happens behind the scenes.
Rate limiting is invisible when it works and infuriating when it is misconfigured. Understanding the underlying algorithms helps you implement limits that protect your API without frustrating legitimate users.

A hardcoded API key committed to a public repo is a nightmare that keeps on giving. Here is a practical guide to managing environment variables and secrets safely across environments.
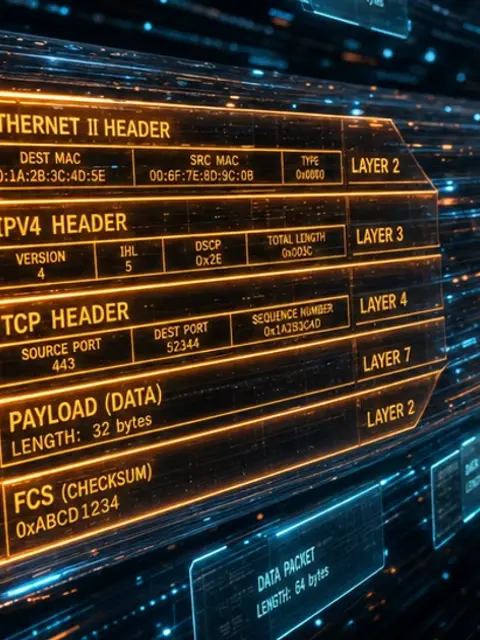
HTTP headers carry critical information about authentication, caching, content type, and security — yet many developers only interact with them when something goes wrong. This reference covers the most important ones.

You type a domain and a page loads — but between those two events is a surprisingly elegant distributed lookup system. Here is exactly what happens at each step.
JSON took over the web API world, but XML still powers enterprise integrations, configuration files, and document formats. Here is a clear-eyed comparison to help you choose the right one.
CSV files look trivial until you encounter a value with a comma inside it, a newline in a cell, or a file saved in the wrong encoding. This post covers everything you need to handle CSV correctly.
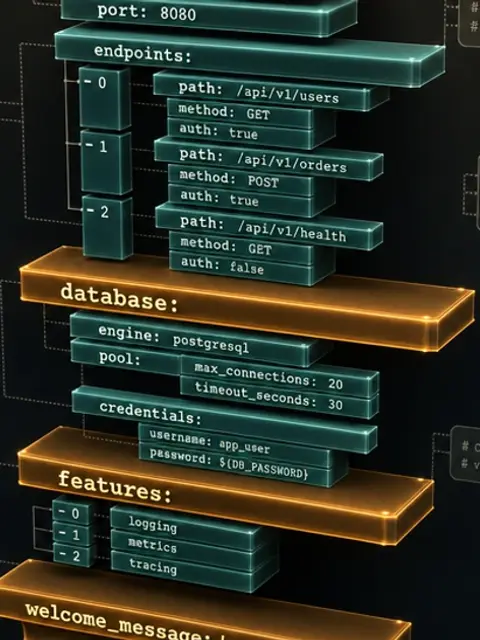
YAML is everywhere in DevOps — Docker Compose, Kubernetes, GitHub Actions, Ansible. Its indentation-sensitive syntax looks clean but has sharp edges. This guide covers the rules you need to know.
TOML was designed to be obvious at a glance — a config format with explicit types and no whitespace sensitivity. Cargo.toml made it famous, but it is now used across the ecosystem.

SQL is one of the most valuable skills a developer can have — and the fundamentals are surprisingly approachable. Start here to write your first real queries confidently.

The choice between SQL and NoSQL is not about which is better — it is about matching the data model to your access patterns. Here is a framework for making that decision with confidence.

An index can turn a ten-second query into a millisecond query — or slow down your writes significantly if misused. Understanding the data structure behind indexes makes both outcomes predictable.
Normalization rules sound abstract until you see what a denormalized table looks like after six months of updates. This guide explains the normal forms using simple, concrete examples.

JSONL puts one JSON object per line, making it streamable, appendable, and easy to process without loading the entire file into memory. Here is why that trade-off matters.
INI files pre-date the internet as we know it — yet Python's configparser, Git's config, and countless system tools still use them. Here is what you need to know about this enduring format.
Markdown is how developers write README files, documentation, and issue comments. Learning the full spec — including the extensions that different platforms add — takes under an hour and pays dividends forever.

Your server already compresses responses with gzip or Brotli — but do you know what those algorithms actually do? Understanding compression helps you optimize assets and set correct headers.

Choosing the wrong image format can double your page weight or break compatibility in older browsers. This guide cuts through the noise with practical guidance for each format.

WebP typically achieves 25-35% smaller file sizes than JPEG at equivalent quality, and browser support is now essentially universal. The case for switching has never been stronger.

SVG is the only image format that is also code — you can write it by hand, animate it with CSS, and scale it to any size without quality loss. Here is what every web developer should know about it.
When you drag a JPEG quality slider from 100 to 80, what actually changes in the file? Understanding the compression algorithm helps you make smarter trade-offs between file size and quality.
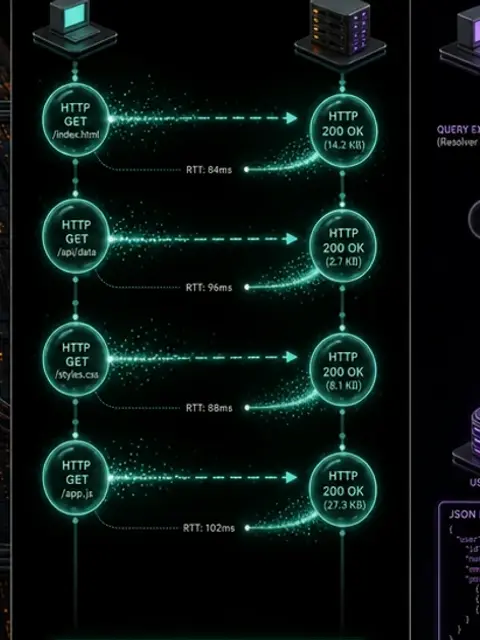
CSS sprites were the standard performance technique for reducing icon HTTP requests in the HTTP/1.1 era. With HTTP/2 and SVG, the calculus has changed — but understanding sprites is still valuable.

Every photo your phone takes embeds GPS coordinates, device model, lens serial number, and timestamp — all invisible but readable by anyone who downloads the file. Here is what EXIF data contains and how to remove it.
RGB and HEX are the same thing in different notations. HSL is much more intuitive for humans. CMYK lives in print. Understanding these distinctions saves you from confusing color bugs.
When you resize an image, your software has to invent new pixel values. The algorithm it uses determines whether the result is crisp, blurry, or filled with jagged artifacts.

Embedding images as Base64 data URIs eliminates an HTTP request but increases file size by 33% and breaks caching. Here is when the trade-off actually makes sense.
Aspect ratios determine how images and videos fill their containers. Getting them wrong causes layout shift and distorted media. CSS now has native solutions that make this straightforward.

CSS specificity is the invisible rule that decides which style wins when two selectors target the same element. Understanding it lets you debug style conflicts without resorting to !important.
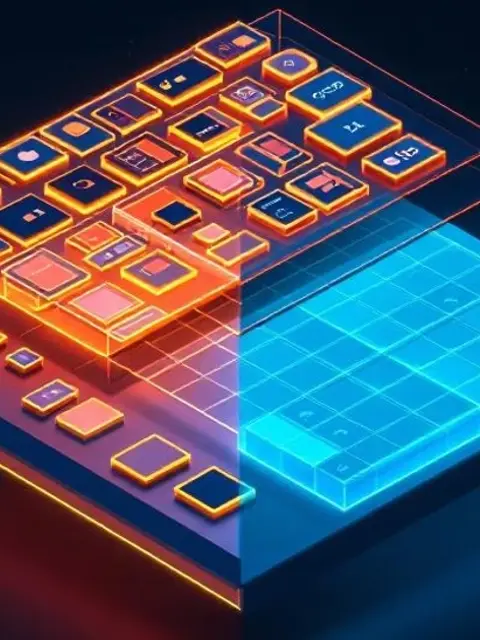
Flexbox and Grid are not competing technologies — they solve different layout problems. Knowing which to reach for makes your CSS cleaner and your layouts more robust.

CSS custom properties are far more powerful than SASS variables — they are live, inheritable, and can be changed with JavaScript at runtime. Here is everything you need to know to use them well.
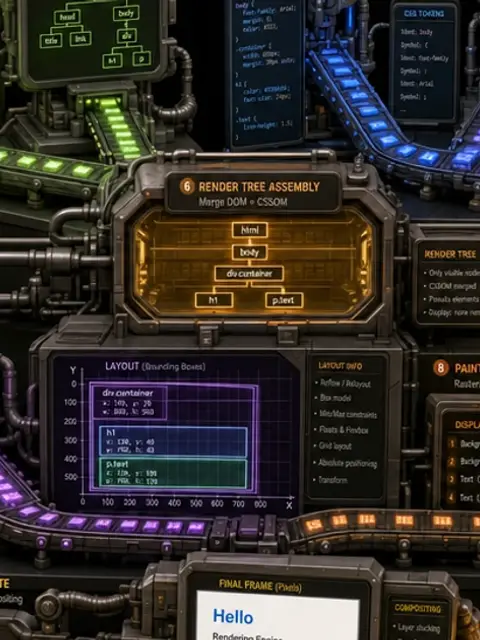
A browser takes HTML, CSS, and JavaScript and turns it into pixels. The steps between those two points — parsing, layout, painting, compositing — directly affect performance and user experience.

The critical rendering path is the sequence of steps a browser must complete before showing the first pixel. Optimizing it is one of the highest-impact things you can do for perceived performance.
Web fonts are one of the most common sources of layout shift and invisible text flash. The font-display property and a few preload hints can eliminate both problems.
CSS minification strips out whitespace, comments, and unnecessary characters without changing any rules. On large stylesheets the savings are significant, and the tooling is trivial to set up.

HTTP caching is one of the most powerful and most misunderstood web performance tools. Getting Cache-Control right can eliminate most of your server's traffic for static assets.

A PDF looks like a printed page but is actually a complex container format with embedded fonts, compressed image streams, and a cross-reference table. Here is what is actually inside.
PDF and DOCX both contain text and images, but they are designed for fundamentally different purposes. Choosing the wrong format causes friction for everyone who receives the file.

A PDF digital signature is not a scanned image of your handwriting — it is a cryptographic proof tied to a certificate. Here is what it actually verifies and what it does not.
Most PDFs are accessibility nightmares — untagged content, no reading order, images without alt text. Making a PDF accessible is not difficult once you understand what a tagged PDF actually is.
A PDF exported from PowerPoint can be 50MB. The same content as a compressed PDF can be under 5MB. Here is exactly what gets compressed and how the algorithms work.
Math.random() and /dev/urandom look similar but are fundamentally different. One is suitable for games, one for cryptography. Understanding why that distinction matters prevents serious security mistakes.

Treating Base64 as encryption or MD5 as a secure hash are among the most common security mistakes developers make. This post draws a clear line between encoding, encryption, and hashing.
Every string in your program is ultimately bytes. Understanding how Unicode maps characters to code points and how UTF-8 encodes those to bytes prevents a whole class of subtle bugs.

Binary is not just for low-level programming — it shows up in bitmasks, permissions, color values, and network addresses. This guide makes number base conversion intuitive rather than mechanical.
Unix timestamps are just numbers — the count of seconds since January 1, 1970 UTC. But timezone handling, milliseconds vs seconds, and the 2038 problem all add complexity that catches developers off guard.

The magic behind HTTPS, SSH, and PGP encryption is public key cryptography — a system where you can encrypt a message that only the intended recipient can decrypt. Here is how it works.

Every HTTPS connection starts with a TLS handshake — a sub-second ceremony that establishes identity and agrees on encryption keys. Here is the full sequence in plain English.

A checksum is a small number computed from a block of data that lets you verify the data has not changed. Here is why this simple idea underpins file downloads, network protocols, and storage systems.
A QR code is a 2D barcode that can store a URL, contact card, or arbitrary text using a grid of black and white modules. Here is how the encoding works and why damaged QR codes still scan.

Lorem ipsum is not random Latin gibberish — it is a mangled passage from a 2000-year-old philosophical treatise that a typesetter scrambled in the 1500s and designers never stopped using.